On this page you can find a selection of articles and tutorials. We recommend the short video tutorials as a quick and effortless way to learn the basics of Cerbero Suite. Make sure to follow us on X and to subscribe to our YouTube channel to keep up with new tutorials.
Short Video Tutorials
The short video tutorials are a quick and effortless way to learn the basics of Cerbero Suite.
In-Depth Video Tutorials
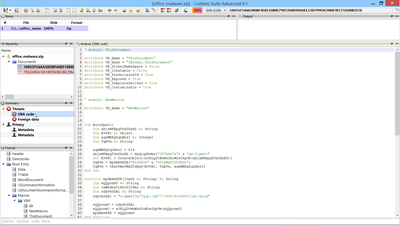
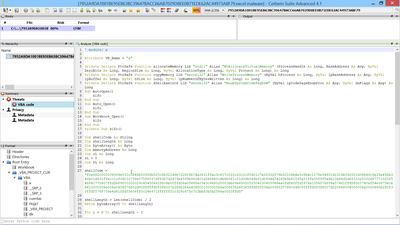
Obfuscated VBA Analysis
You can find the scripts used to analyze this malware on our blog.
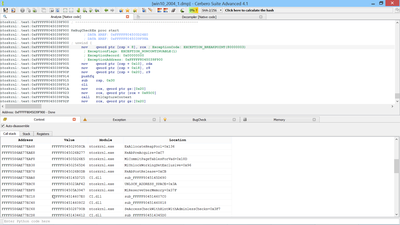
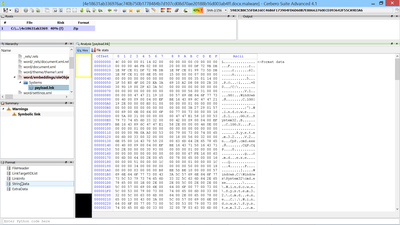
Malicious Windows Link with Embedded Microsoft Cabinet Analysis
You can find the original analysis for this malware on malwarebytes. As a bonus, in the video we show how to improve the static analysis of the final payload by resolving API calls. You can find the script code on our blog.
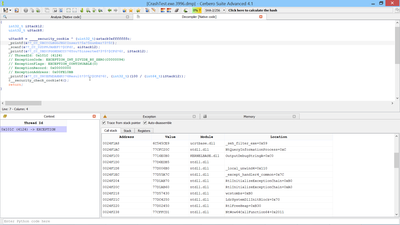
Malicious Excel Document Analysis
A first introduction to our Silicon Excel Emulator and how to analyze malicious Excel documents.
QakBot Excel Malware Analysis Series (2nd sample, 3rd sample)
In this video-series various samples of malicious Excel vectors belonging to the QakBot malware are analyzed. You can find the script code for the first sample and the second sample on our blog.
Self-Decrypting Excel Malware Analysis
A more advanced Excel malware which uses a time-based value to decrypt its own formulas. You can find the script code mentioned in the video on our blog.
Obfuscated Excel Malware Analysis
An introduction to the formula view which in conjunction with our Silicon Excel Emulator is used to analyze an obfuscated Excel (XLSX) malware in just 50 seconds.
In-Depth Articles
InQuest: Cerbero Suite: The Hacker’s Multitool
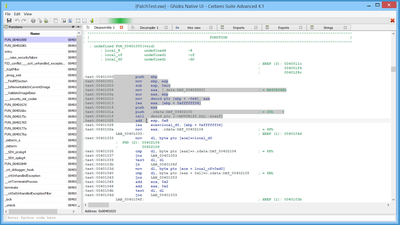
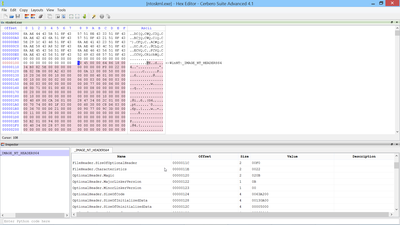
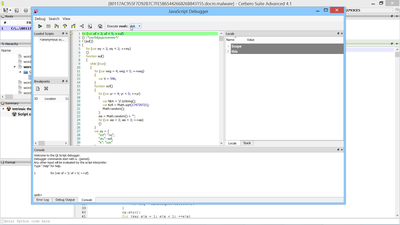
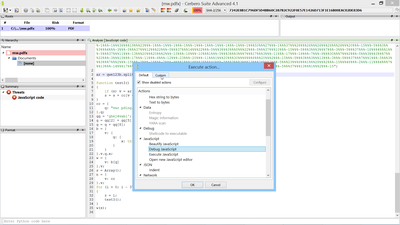
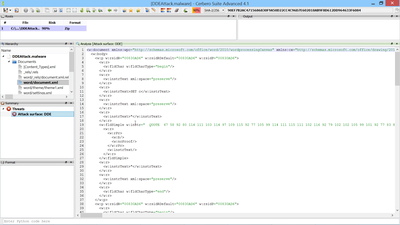
Analysis of a multi-stage Microsoft Office malware containing VBE, CAB and heavily obfuscated JSE. The article shows how to analyze the various stages and completely deobfuscate the JavaScript code.
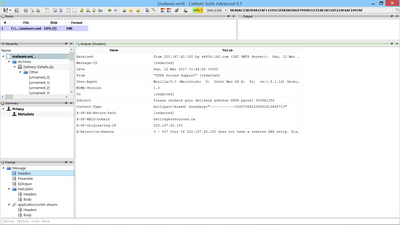
Yet another PDF/XDP Malware
An in-depth analysis of a malware using XDP embedded in a PDF and anti-analysis tricks.
PDF/XDP Malware Reversing
An in-depth analysis of a malware using XDP with JavaScript embedded in a PDF document.
Analysis of CVE-2013-3906 (TIFF)
An in-depth analysis of an office document which uses a TIFF vulnerability to execute shellcode. The article includes the analysis of the shellcode and of the payload.
Raw File System Analysis (FAT32 File Recovery)
This article shows how to perform raw analysis of a file system by using C types imported from source headers. The gained knowledge is then used to write a small utility in under 300 lines of Python code to recover deleted files.
Disclosure: Creating undetected malware for OS X
A proof-of-concept which demonstrates how to create undetected malware on OS X by using the internal mechanism called Apple Binary Protection. At the time of writing, all security solutions were tricked by this technique.
Risikofaktoren bei verschiedenen Dateitypen (German)
An easy-to-read overview (in German) of the main risks associated to different file types. The paper tries to increase the awareness of end users. It contains statistics and best practices.
BlueBox Android Challenge
A crackme which offers the opportunity to show how to reverse engineer protected Android applications with Profiler.
The security of non-exec files
This article is based on a speech given at DeepSec. It tries to sum up the main risks associated to non-executable files, meaning those files which are generally viewed as harmless by the user.
SDK Tutorials
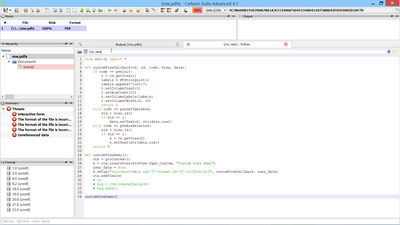
Command-line scripting
In Cerbero Suite you can write scripts to be executed from the command-line. This is extremely useful as it enables users to create utilities using the SDK and to integrate them into their own tool-chains.
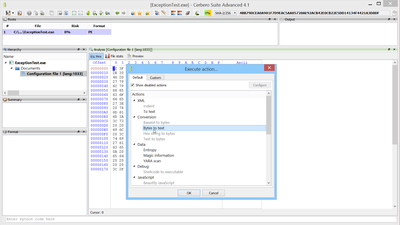
How to write Custom Actions
Actions are one of the basic elements of Cerbero Suite. Writing new actions is trivial and this tutorial shows you how to do it.
First introduction to the SDK
This tutorial introduces some basic concepts of the SDK. In particular it explains some basic classes and the programmatic use of filters. The part relative to PySide is obsolete, since Cerbero Suite allows you to write complex UIs using its own SDK.
PDF, Office, Java, Flash & DEX
A first introduction on how to access these file types from our Python SDK. It shows how to traverse objects in documents and how to disassemble byte-code.
Extension: Key Providers
Key Providers are a convenient way to provide keys through scripting to files which require a decryption key (e.g. an encrypted PDF). Through Key Providers you can load your own dictionaries for decryption.
Extension: Hooks
Hooks are a very powerful extension which allows you to change the behavior of existing scan providers. This is just a short introduction: there are many more ways to use Hooks!
Detect broken PE manifests
This is a small example of a Hook used to detect broken manifests inside of PE files.
Extension: Logic Providers
Logic Providers are quite similar to Hooks: the callbacks are named the same. Their purpose however is different. Hooks are very powerful, but their purpose is to modify the behavior of scan providers. Logic Providers, on the other hand, tell the scan engine which folders to scan, which files, etc. You need Logic Providers to create your own tools.
Extension: Scan Providers
Scan Providers are the most important type of extension as they allow you to add support for new types of file types. You can check out our open-source Scan Providers to learn more about how to write one of your own.
Extension: Packages
How to install, uninstall, verify and create installable packages for extensions. Packages are made in a way that makes writing setup code unnecessary for the majority of cases.
A brief introduction to Custom Views
Custom views are fundamental to create complex views with all types of controls. They rely exclusively on our SDK with no external dependencies.
Parameters & Settings
If you want to ask the user to enter parameters or settings, a dialog with a property editor is an easy way to do it. Cerbero Suite offers a simple API for these situations.
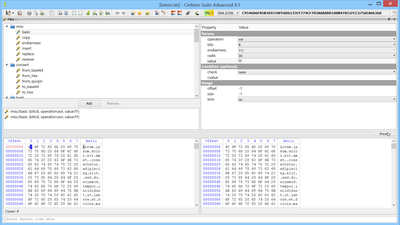
C++ Types: Introduction
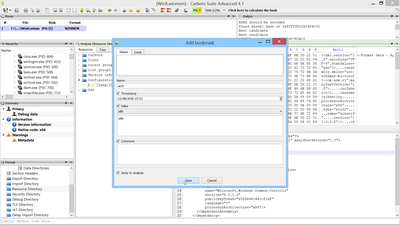
Cerbero Suite gives you the ability to import C++ types such as classes and structures. This tutorial is a first introduction into this vast topic.
C++ Types: Under the Hood
This tutorial goes fully in-depth into C++ Types: it covers complex topics such as inheritance, vtables, bit fields, packing, field alignment, templates and much more.
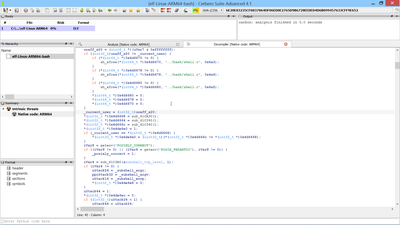
Dissecting an ELF with C++ Types
In this tutorial C++ Types are used to programmatically dissect an ELF binary.
Stripping symbols from a Mach-O
As an example of a command-line utility this tutorial shows how to write a small Python script to strip symbols from a Mach-O binary. There’s also another tutorial demonstrating the same process for an ELF binary.
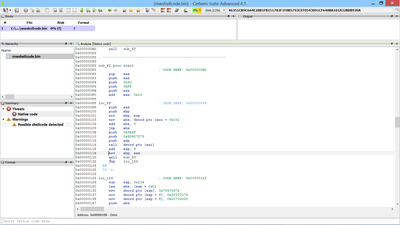
String decryption with Carbon
A brief introduction to the SDK of our Carbon Disassembler showing how to decrypt strings in a disassembly using two different approaches.
Theme support
If you want to write a new UI theme for Cerbero Suite or change an existing one, then this tutorial is what you’re looking for!
Custom filters: Lua and misc/basic
Introduction to filters written in Lua. Lua filters can cover cases which cannot be handled by built-in filters.